How Blockchain Transactions Get Verified and Stay Secure
A blockchain has no central authority.
There is no bank approving transactions. No company maintaining the ledger.
So how does the network decide which transactions are valid?
The answer is a system called a consensus mechanism.
Consensus mechanisms allow thousands of independent computers to agree on the same transaction history without trusting one another.
But verification is only part of the story.
The deeper question is this: why is the system hard to attack?
What Is Consensus?
Consensus means agreement.
In a blockchain, nodes must agree on:
- Which transactions are valid
- The order of transactions
- The current state of the ledger
Without consensus, users could attempt to spend the same funds twice. This is known as double spending.
Because public blockchains are open networks, anyone can submit transactions. The system therefore needs a way to verify activity objectively.
Consensus mechanisms solve this problem using rules, incentives, and cryptography rather than central oversight.
Agreement is not based on trust in a single party. It is based on processes that anyone can verify.
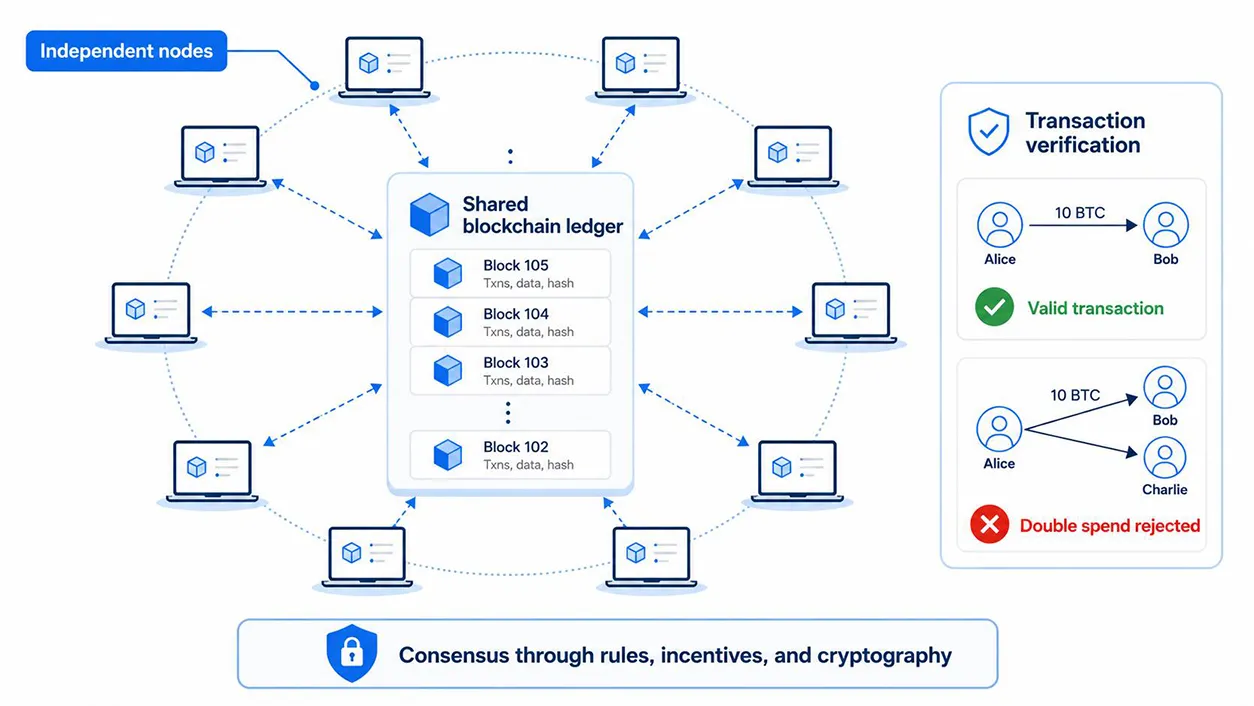
Verification Is Only Step One
Verifying a transaction is relatively simple.
The network checks:
- Does the sender have the funds?
- Has the transaction been signed correctly?
- Has this money already been spent?
The harder problem is preventing someone from rewriting history after the fact.
This is where blockchain security comes from.
It is not just about checking transactions. It is about making manipulation extremely costly.
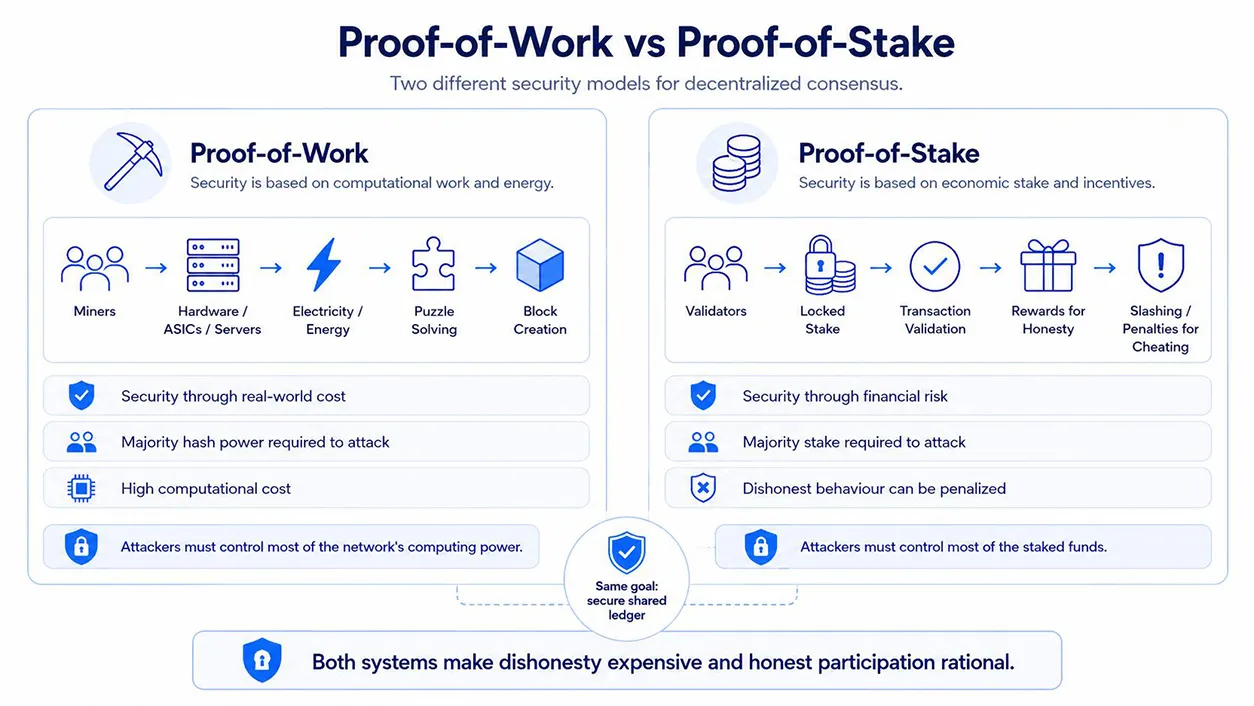
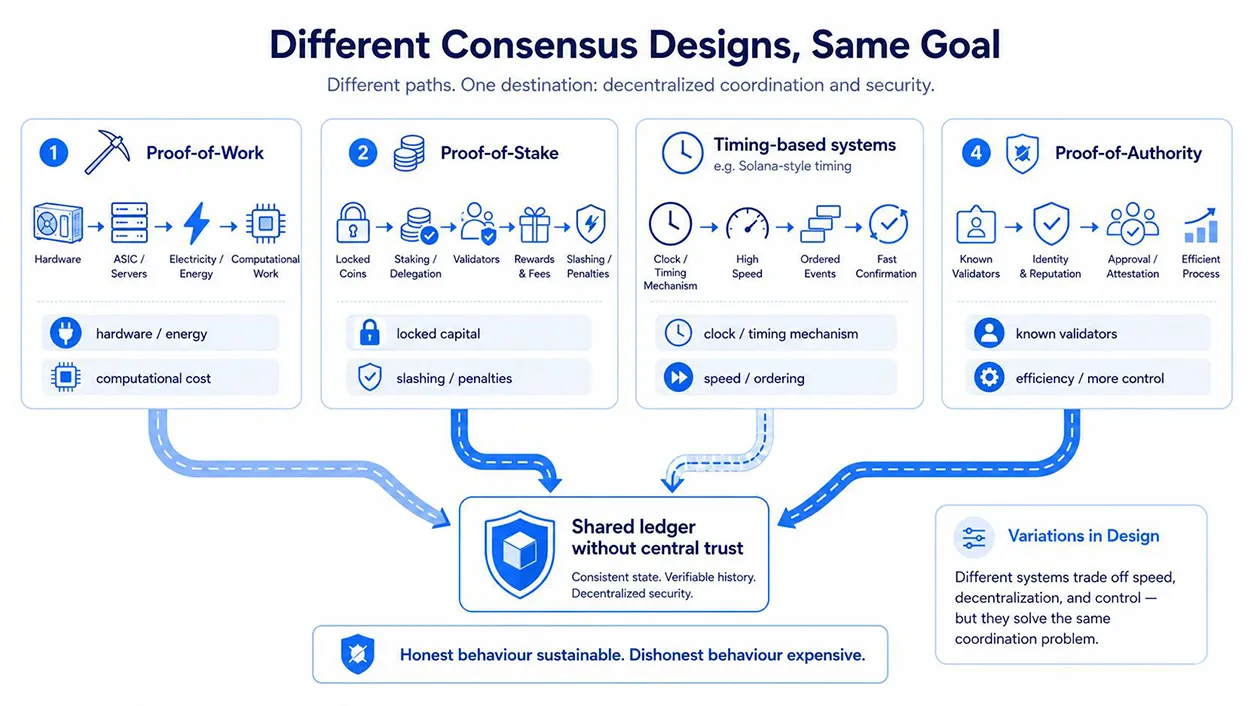
Proof-of-Work (PoW)
Proof-of-Work, used by Bitcoin, secures the network through computation.
Miners compete to solve mathematical puzzles. The winner adds the next block.
This process requires energy and hardware.
That cost creates protection.
To change past transactions, an attacker would need to control most of the network’s computing power. That would require enormous investment.
In this model, security comes from real-world cost.
Proof-of-Stake (PoS)
Proof-of-Stake, used by Ethereum, secures the network through capital.
Validators lock up funds and are selected to confirm transactions.
If they act honestly, they earn rewards.
If they cheat, they lose their stake.
In this model, security comes from financial risk.
Attacking the network means risking large amounts of capital, which can lose value during the attack itself.
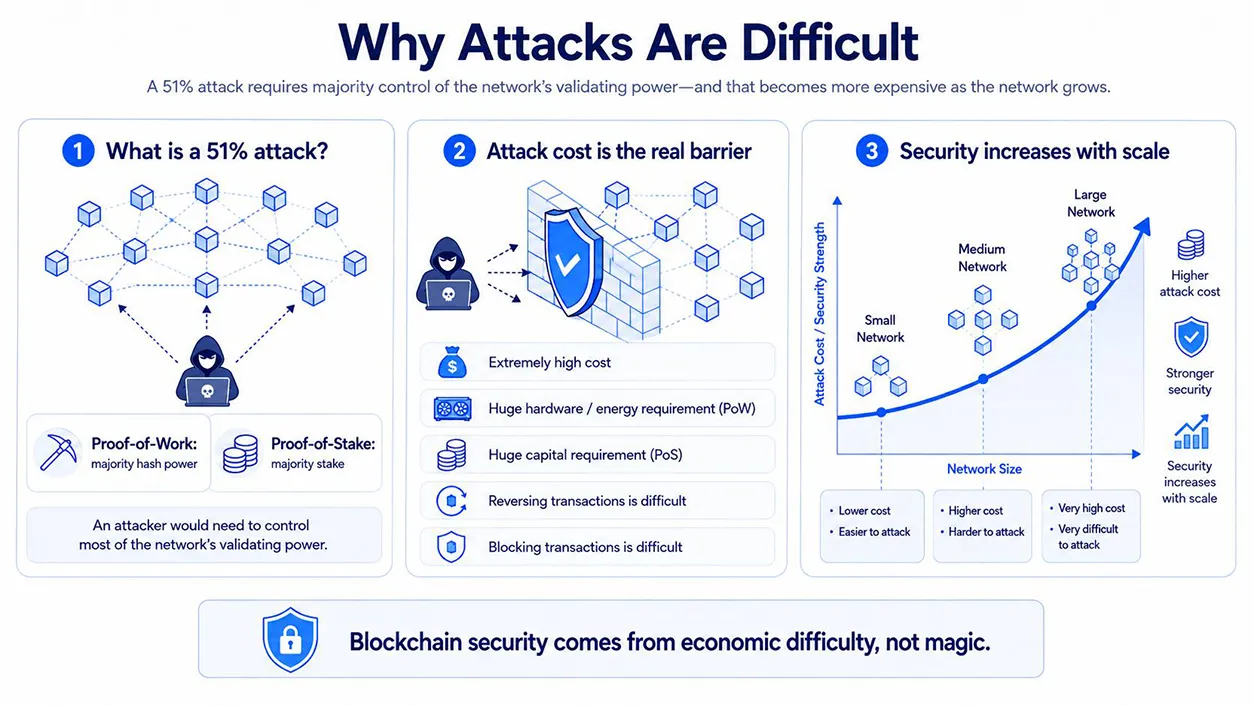
Why Attacks Are Difficult
When people talk about blockchain security, they often mention a “51 percent attack.”
This means controlling a majority of the network’s validating power.
In Proof-of-Work, that means most of the computing power.
In Proof-of-Stake, that means most of the staked funds.
With that control, an attacker could attempt to reverse transactions or block new ones.
But the key point is cost.
Acquiring that level of control is extremely expensive.
The larger the network, the higher the cost.
Security increases with scale.
Incentives Keep the System Honest
Blockchains do not rely on trust. They rely on incentives.
Participants follow the rules because it is profitable to do so.
- Honest behaviour earns rewards
- Dishonest behaviour leads to losses
This creates a system where cooperation is the rational choice.
If the incentives are designed correctly, attacking the network becomes less attractive than supporting it.
This is why blockchain security is often described as economic security, not just technical security.
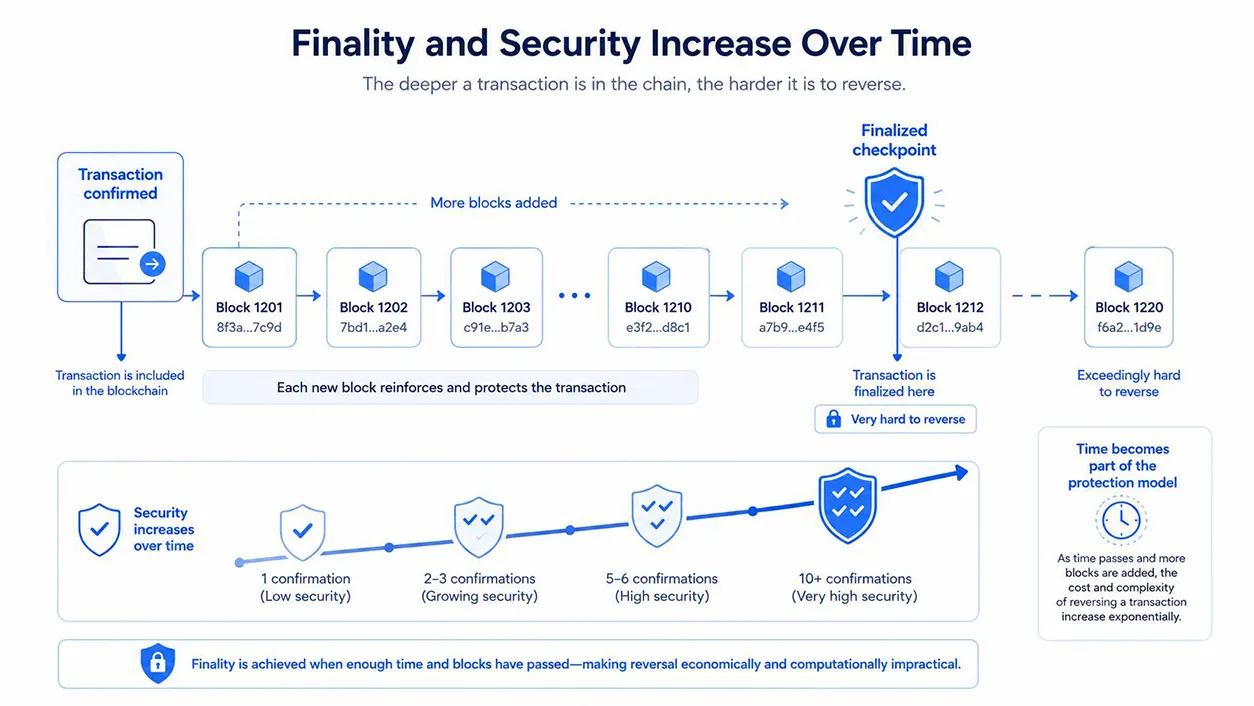
Finality and the Role of Time
Security is not instant. It builds over time.
When a transaction is first added to a block, it is considered confirmed.
As more blocks are added after it, reversing that transaction becomes harder.
This is known as finality.
In Proof-of-Work systems, finality increases gradually. Each new block strengthens the previous ones.
In Proof-of-Stake systems, some networks introduce checkpoints where transactions become final and cannot be reversed without severe penalties.
Time becomes part of the protection model.
The deeper a transaction is in the chain, the more secure it becomes.
Variations in Design
Different systems adjust how they reach consensus.
For example, Solana uses additional timing mechanisms to improve speed.
Other systems, such as Proof-of-Authority networks, rely on known validators for efficiency.
These variations change performance and control, but the core idea remains the same.
Make dishonest behaviour expensive and honest behaviour sustainable.
The Takeaway
Blockchains do not rely on central authorities to verify transactions.
They rely on systems that make cheating difficult and cooperation profitable.
Proof-of-Work uses computational cost.
Proof-of-Stake uses financial risk.
Other systems introduce variations for speed or control.
All of them aim to solve the same problem.
How to maintain a shared system where no single participant needs to be trusted.
Security in blockchains does not come from secrecy.
It comes from cost, incentives, and transparent rules.
That is what allows strangers to coordinate at scale without central control.